Table of contents
TL;DR / Geek Summary:
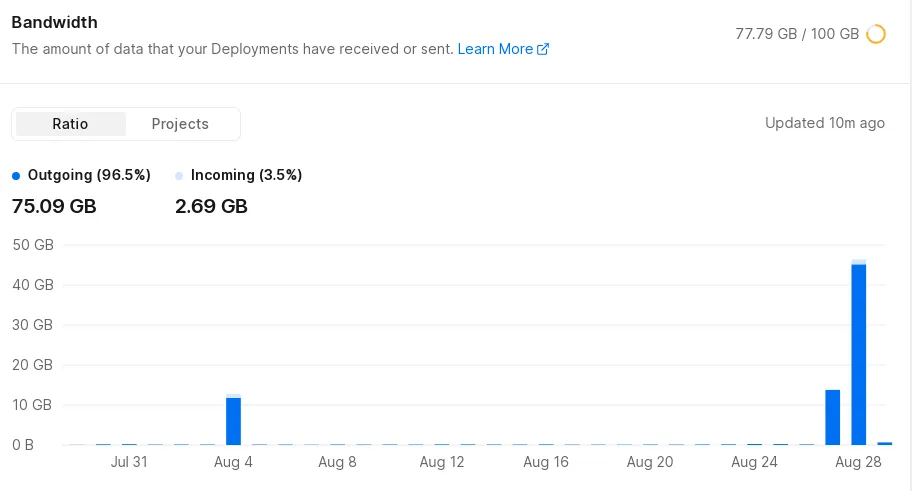
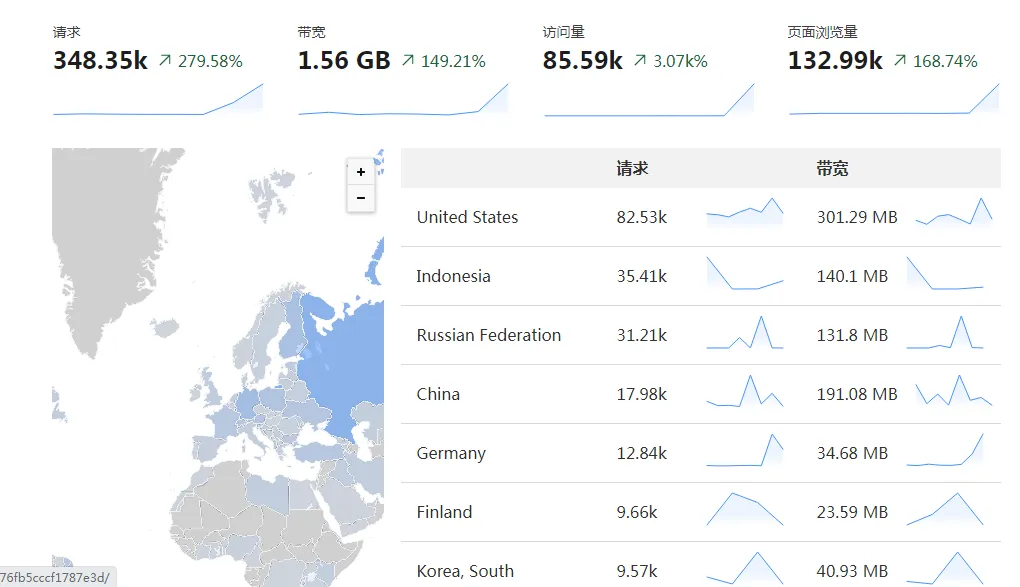
- Threat Intel: Sustained 4-day malicious DDoS/CC assault consuming 75GB+ bandwidth in hours.
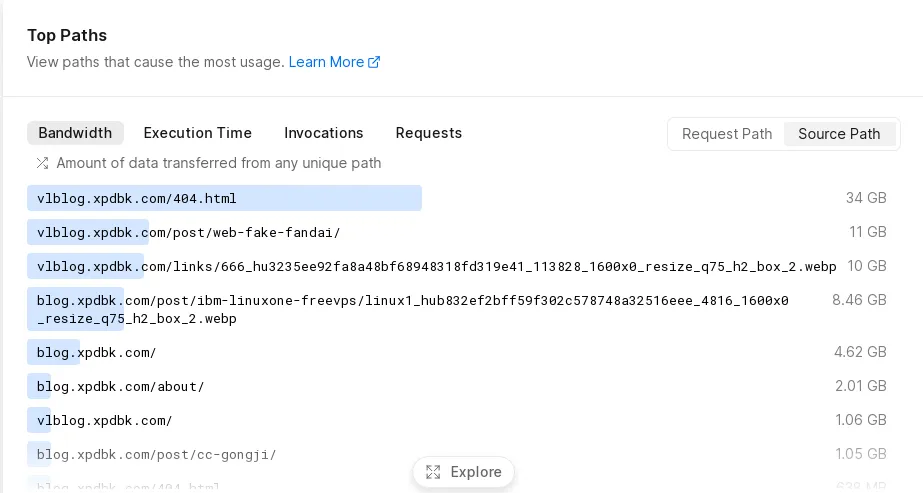
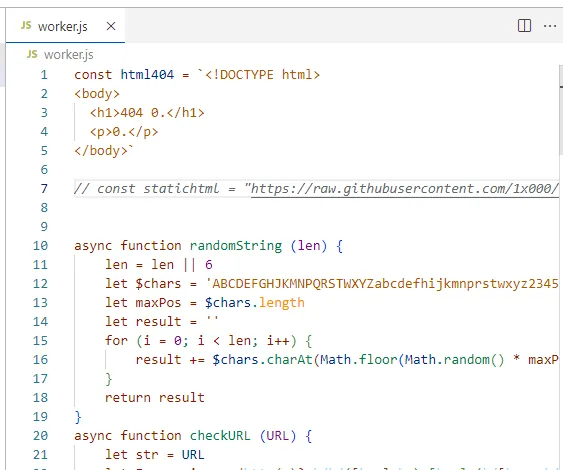
- Attack Vector: Mirror link injection via shortcode service and volumetric HTTP floods.
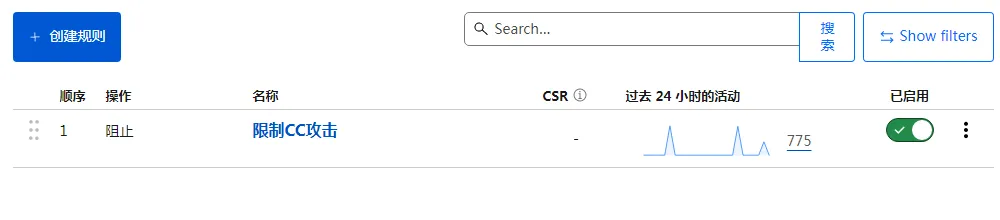
- Mitigation: Deployed Cloudflare CDN (Orange Cloud) and WAF firewall rules to neutralize traffic.
# Introduction
Because I originally built my blog using wordpress, I am very familiar with DDoS and CC attacks and have always paid close attention to them. Later on, I successively tried dynamic frameworks like typecho and Halo, then moved from jekyll to Hexo, before finally settling on Hugo, a static blog framework. After that, I stopped worrying about server and DDoS protection issues and remained in a completely worry-free state. That is, until a certain person recently launched a malicious 4-day attack on my website, which forced me to take DDoS and CC protection seriously again.
# How It Started
Around 11 PM, while I was scrolling through my phone, an email arrived telling me my website had already used 75GB of bandwidth. I thought to myself: what on earth used up so much bandwidth?
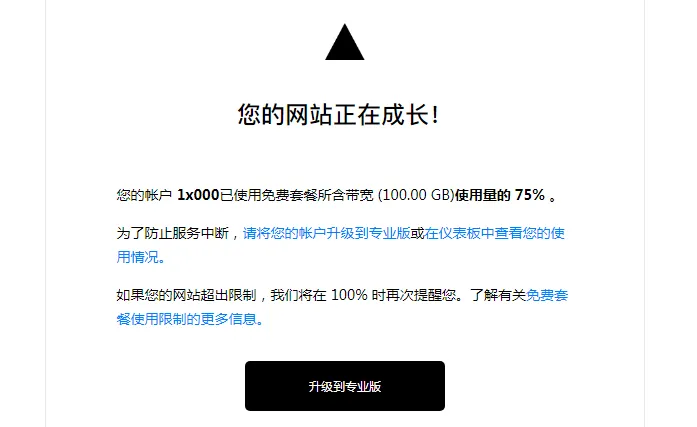
Then I clicked in to take a look, and it literally gave me a jump scare.
If I ignored this, my site would definitely be forced to shut down. And once it’s shut down, I would lose all my search engine indexing.
# Interlude
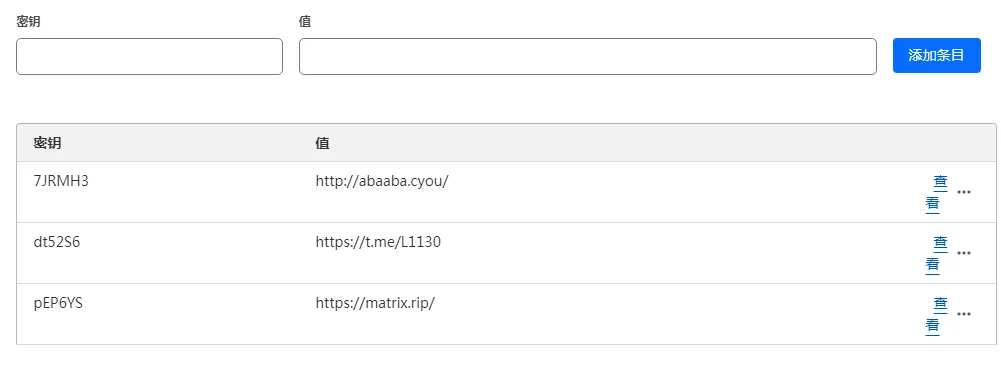
This attacker also stuffed a ton of gray-market (illicit) links into my URL shortening service. However, thanks to my HTML modifications to hide the input form, visiting https://l.xpdbk.com doesn’t allow anyone to add links; only I can add them from the backend. I originally intended to make the service available for public use, but because people like this exist, I had no choice but to make it private.
# Taking Action
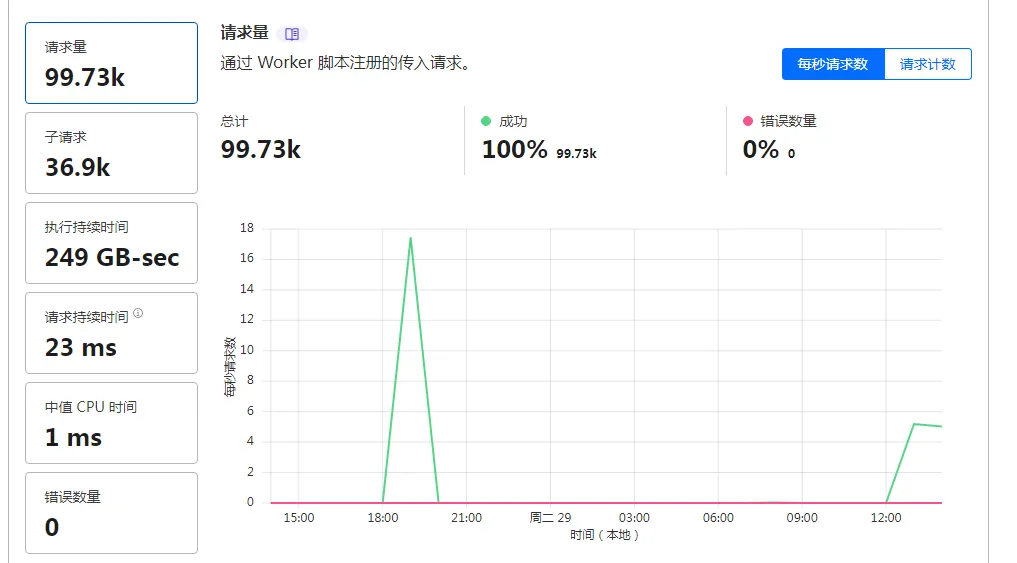
I quickly rushed to enable CF CDN. I hadn’t turned on the little orange cloud for Cloudflare CDN before because I wanted to accommodate loading speeds for users in China. Blocked by the WAF firewall, all of the attacker’s traffic was successfully mitigated.

# Conclusion
All the malicious traffic was completely neutralized.
A word of advice for the attacker: In this world, you can’t get something for nothing.